The process of encryption and authentication go together to creating a secure environment. For organizations, authentication is vital as it allows them to keep the networks secure as it permits authenticated users only for accessing its protected resources. We have the best experts who can provide you with the highest quality assignment writing help on Encryption and Authentication Techniques and our professionals can provide you with the best grades.
Using Encryption and Authentication Techniques
Encryption and Authentication techniques are used in our daily lives. These are discussed in our Encryption and Authentication Techniques homework help online as follows:
- Encryption technique is used if a person purchases tickets online. Encryption is used for protecting the personal information and credit card information of the person when it is sent online on the internet. The company’s data is encrypted by the company.
- An authentication technique is used when a person shows his ticket at the airport. The ticket is shown so that he can get the boarding pass. Airports should authenticate that the person who has shown the ticket is the person who has bought it before giving boarding pass to him.
- Encryption should be used when people provide their personal information for registering something or purchasing a product. This way the privacy of a person is ensured. This technique is used when the data given to the client by the server should be protected including test results and financial statements.
- Authentication must be used whenever a person wants to know who is viewing or using his site. Many commercial websites need people to log in prior to purchasing products so that they know the actual purchasers.
How Does Encryption Authentication Work?
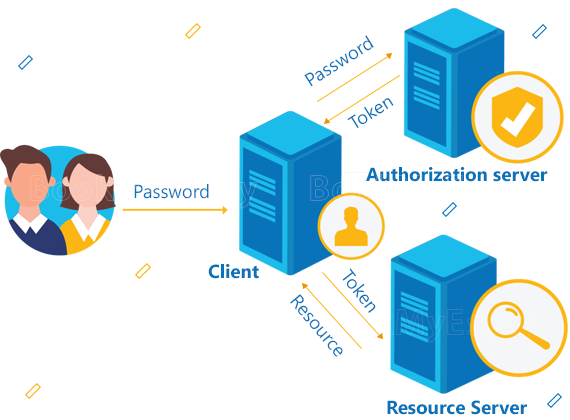
When you protect a file on the computer, which is not connected to anything then the encryption authentication technique is easy. You have to encrypt the file, keep safely the key, and you shall be secure. In cloud applications, authentication is difficult. The applications use public-key encryption that uses two keys; one key is used for encrypting the data and the other key is used for decrypting the data.
The public key is available publicly, though the private key should be kept secret. In email encryption, you have to obtain the public key of the recipient and use the key for for encryption. As the private key is kept confidential, they can decrypt.
Encryption authentication prevents attacks using digital signatures. The authority confirms that the key and signature are authentic. For making encryption authentication highly secure, a Certificate Authority is used for verifying all parties and it handles encryption management automatically. The complete process is explained when you buy online assignment help on Encryption and Authentication Techniques.




 3 Bellbridge Dr, Hoppers Crossing, Melbourne VIC 3029
3 Bellbridge Dr, Hoppers Crossing, Melbourne VIC 3029

